Asset Management
Risk Cloud’s Asset Management Application centralizes key asset information and workflows in one location. Easily monitor critical assets,…
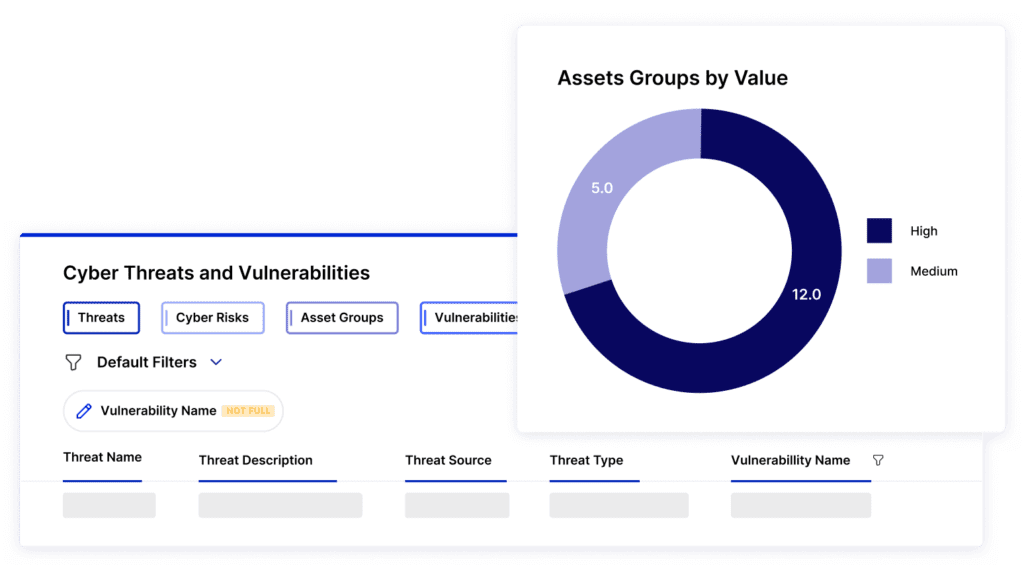
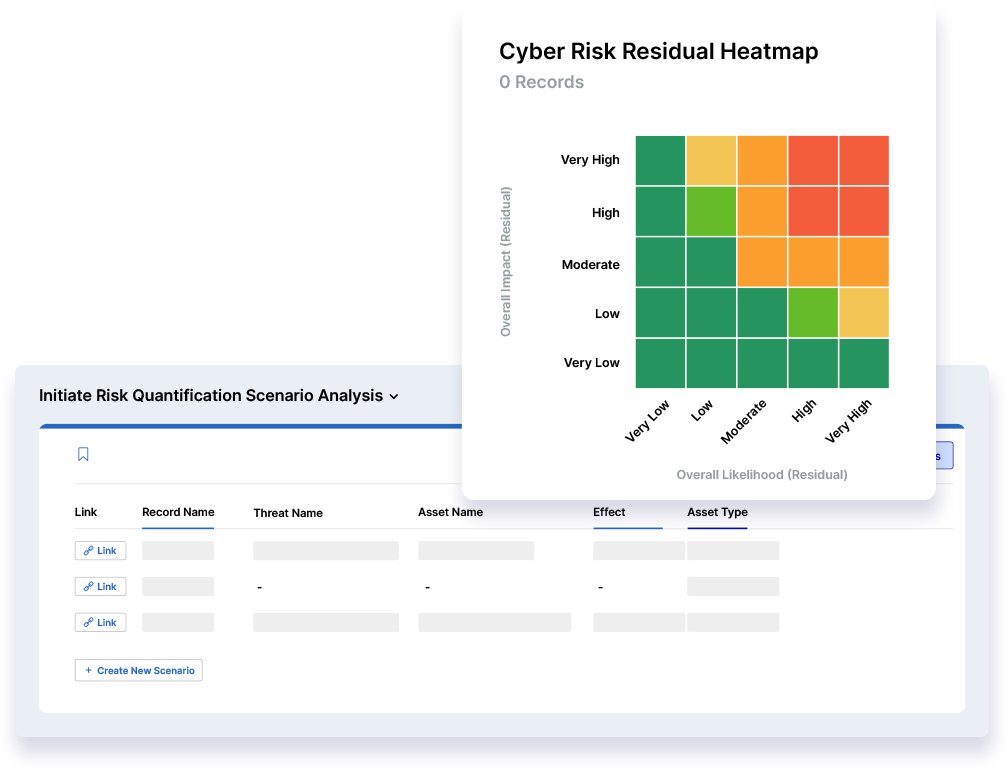
Risk Cloud®’s Cyber Risk & Controls Compliance Solution links cyber threats to business impact, so you can add context to any decision, prioritize remediation, and report what matters most to your key stakeholders.
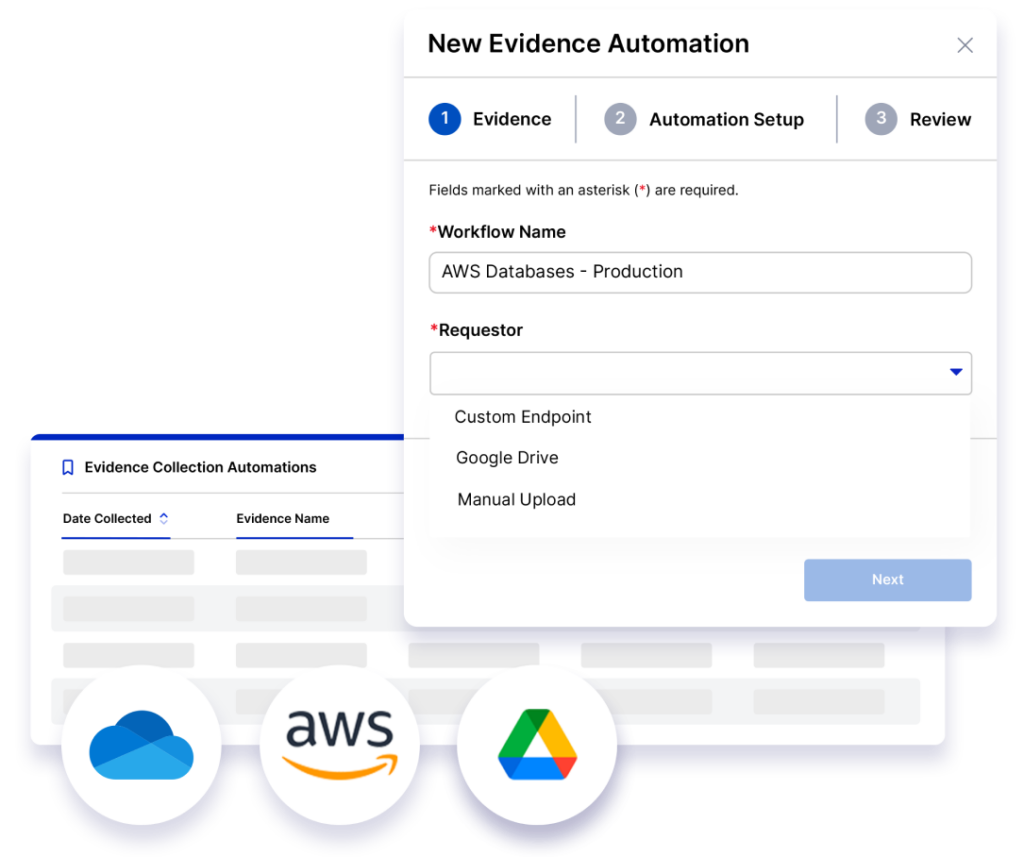
Do more with less by automating cyber risk assessments, control evidence collection, reminders, and escalations. Then, boost collaboration by integrating workflows with the tools risk and controls owners love most like Jira, Slack, and Microsoft 365. With more time and insights to connect cyber risk to business impact, your team can spend less time on tedious workflows and more time maturing your organization’s cyber risk management strategy.
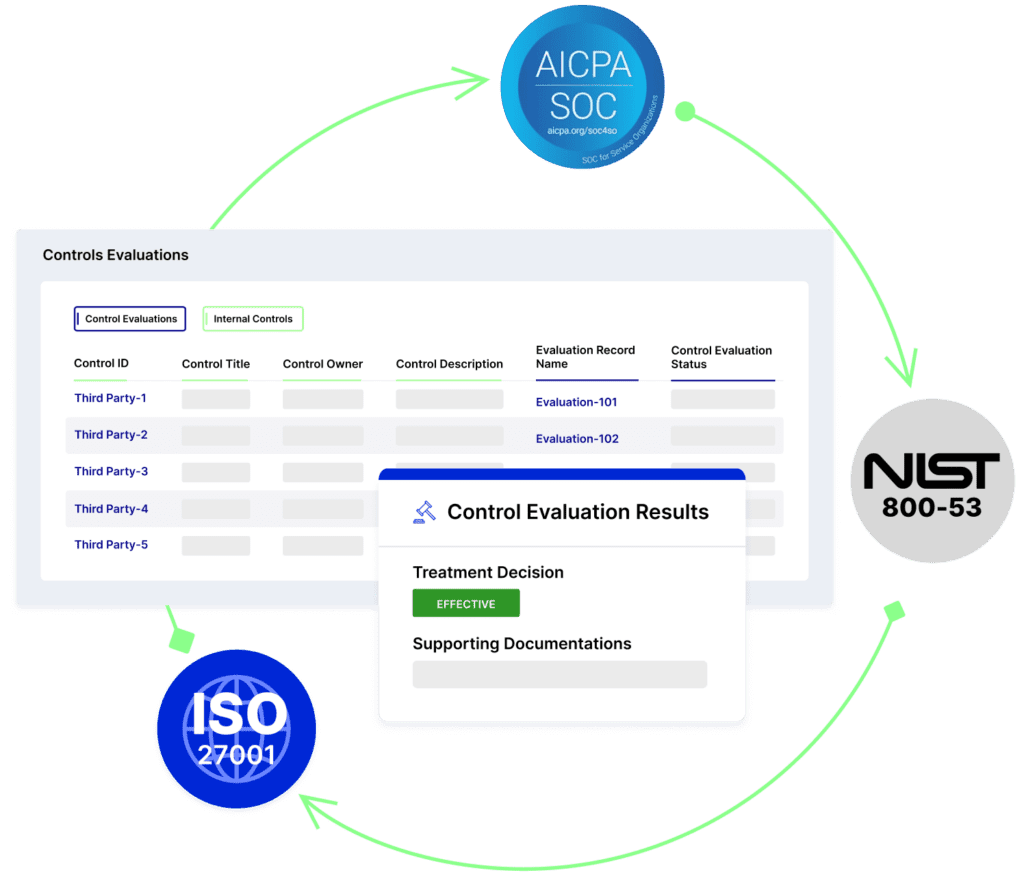
Get deeper visibility into cybersecurity risk across your enterprise and stay audit ready with a connected view of critical assets, risks, and controls. Create a single source of truth for assessing gaps and redundant requirements across 20+ control frameworks and regulations with the Risk Cloud Controls Repository.
Risk Cloud’s Controls Compliance and Cyber Risk Management Applications integrate with tools like ServiceNow™ and Tenable® to help you identify assets at risk and prioritize your response. Quickly uncover ineffective or broken controls and take action to reduce risk exposure.
Deepen stakeholder understanding and engagement with reports and dashboards aligned to their top priorities. Risk Cloud combines qualitative and quantitative cybersecurity risk insights from every business unit, so you can share findings and prioritize response across your entire organization.
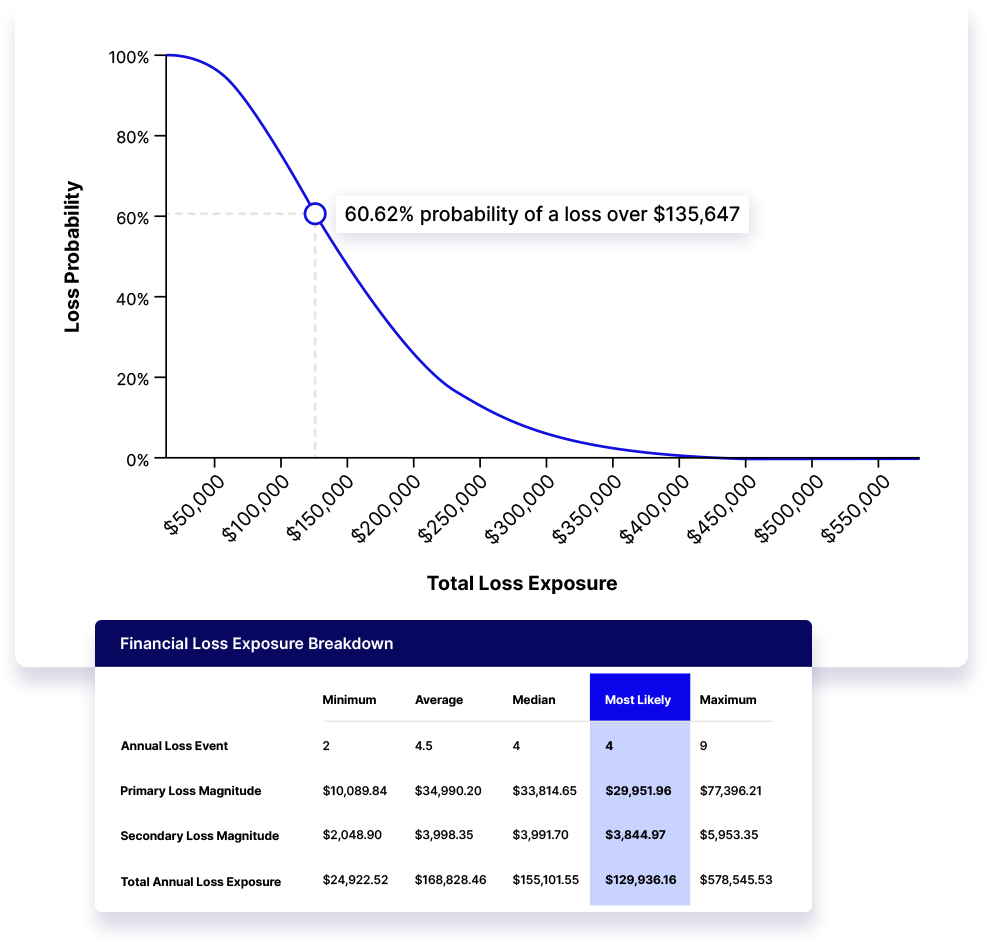
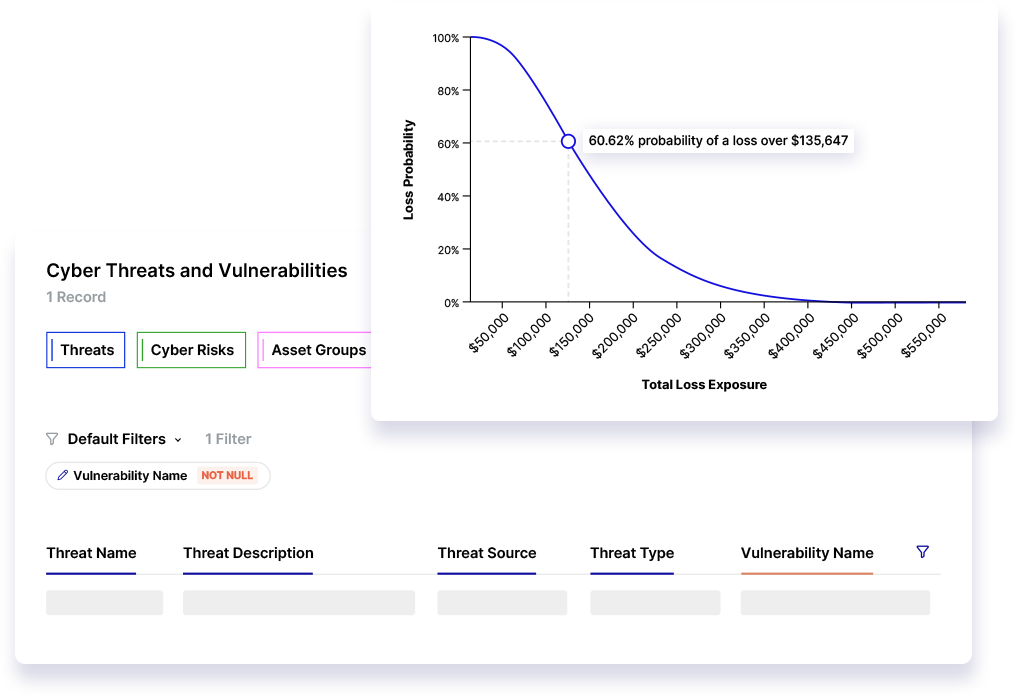
Risk Cloud Quantify® enhances traditional quantification techniques with Monte Carlo simulations and supports the Open FAIR™ Model. Translate the business impact of cyber risk into financial terms to easily communicate the benefits of your program with insights from a single, integrated cyber risk management platform.
Our Cyber Risk & Controls Compliance Solution includes everything you need to manage cyber risk at scale.
- Josh H, Analyst, Vendor Management

- Tom S, Senior Information Security Analyst

- Paul H, VP of Business Continuity Management

- Andrew C, CFO

- Erin H, Corporate Compliance and Enterprise Risk Management Business Analyst

Our Cyber Risk & Controls Compliance Solution includes two Power User licenses. Power User licenses include full build and manage permissions for the individuals managing your risk management program. Don’t worry about budgeting for your entire organization – all other user licenses are included with every subscription.
Risk Cloud’s Cyber Risk & Controls Compliance Solution maps to 20+ trusted frameworks like the NIST Cybersecurity Framework, NIST 800-53, and the CIS Top 20. You’ll also have access to every framework, standard, and regulation inside the Risk Cloud Controls Repository.
You’ll receive two Standard Implementations to help you quickly get up and running with your Cyber Risk Management and Controls Compliance Applications. Our client success and implementation teams will guide you every step of the way to shorten time-to-value and maximize your investment into Risk Cloud. Read our reviews on G2 to learn why 98% of Risk Cloud users report satisfaction with our customer support.
Yes! In addition to Power User Certification for your team, you’ll get access to LogicGate’s Fundamentals of FAIR course to learn the basic principles of FAIR methodology and risk quantification in Risk Cloud.
Yes! With risk management Applications for every use case and 100s of integration capabilities, the Risk Cloud platform can help you centralize and streamline risk management functions across your enterprise to eliminate data silos, improve cross-team collaboration, and help you make more strategic decisions. Request a custom quote to explore holistic risk management solutions for your organization.
Cybersecurity leaders like you also recommend:
Risk Cloud’s Asset Management Application centralizes key asset information and workflows in one location. Easily monitor critical assets,…
Stay ahead of the most critical vulnerabilities in your environment by streamlining and centralizing your pentesting process with…
Vulnerability Management Application helps organizations manage and assess the vulnerability impact.
Cyber attacks are up 38% in the last year, and they’re getting more costly. Do you know how…
As a company grows, so does its responsibility for keeping its customers’ data and assets safe and secure.…
The EU AI Act marks a significant step towards regulating artificial intelligence, setting a global standard for AI…
AI has exploded onto the tech scene in the last year, bringing with it huge promises and potential.…
The pressure to leverage generative AI to enhance business performance is a critical priority for most companies today. …
