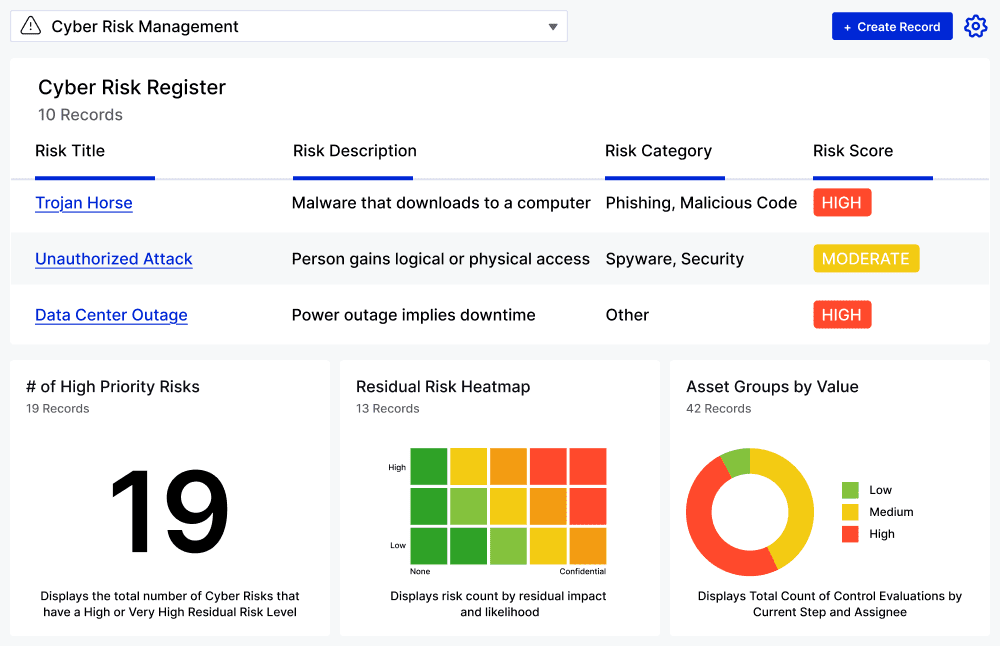
Cyber Risk Management Application
Assess and mitigate cyber risks effectively with a centralized platform that connects assets, threats, and vulnerabilities, automating your risk management processes.
What is the Cyber Risk Management Application?
The Application helps organizations identify, assess, and mitigate cyber risks effectively. It centralizes risk information, automates assessments, and enhances collaboration across teams. With real-time reporting and insights, organizations can make informed decisions to protect their assets and ensure compliance with relevant regulations.
Streamline Your Cyber Risk Management Program
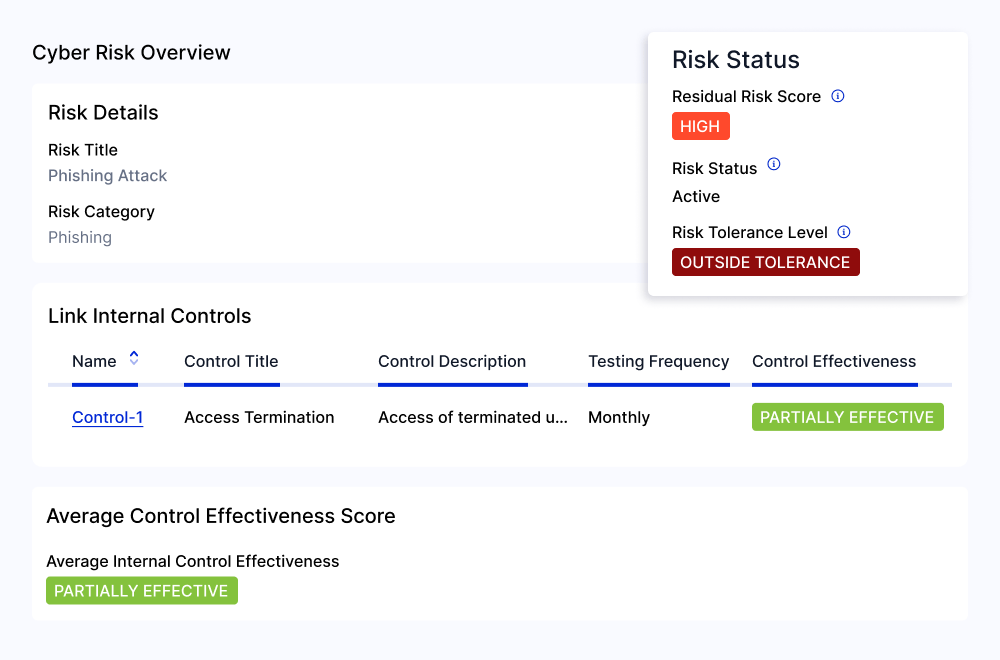
Implement an automated cyber risk management program with pre-built assessment workflows based on NIST 800-30 best practices.
Prioritize Cyber Risk Mitigation Based on Vulnerability Criticality
Integrate with leading technologies to dynamically connect assets, threats, vulnerabilities, and controls to identify at-risk assets and prioritize mitigation efforts Additionally, out-of-the-box integrations with popular communication tools streamline workflows and automate your team’s response to threats.
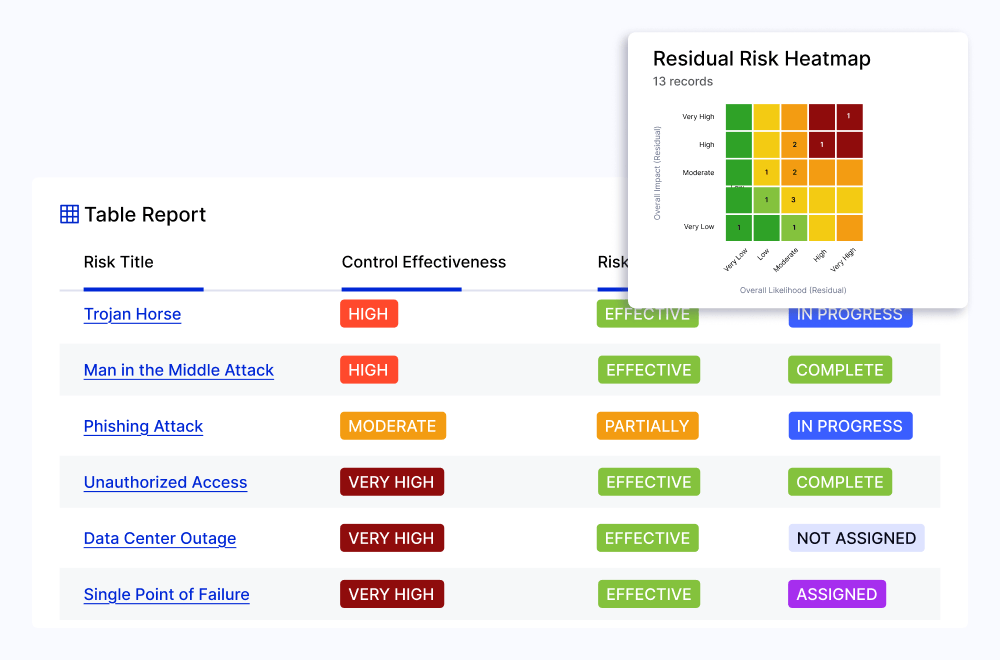
Streamline Reporting and Optimize Resource Allocation
Organize assets by type or business criticality and categorize vulnerabilities by severity or risk threshold. This approach enables your team to concentrate on the most critical issues, reducing noise in reporting streams and enhancing overall focus.
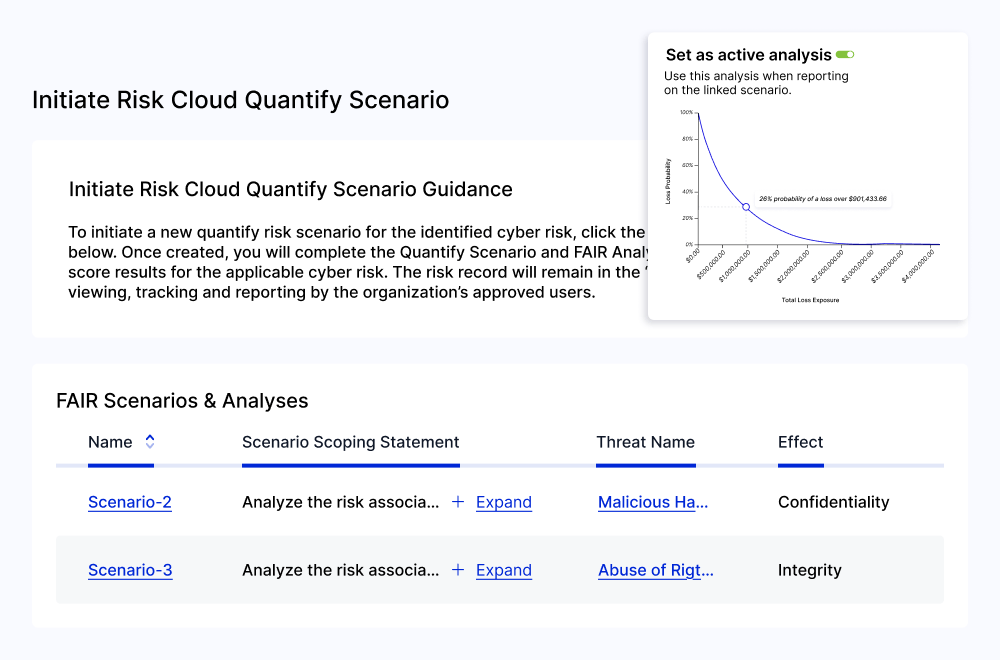
Translate Cyber Risk into Financial Impact
Balance the potential financial impact of risk remediation with maintaining regulatory compliance. Manage your cyber risk posture effectively with a comprehensive Control Repository that connects and automates workflows for NIST, ISO, CMMC, and SOC 2 standards to streamline compliance processes and enhance your organization’s security posture.