In the rapidly evolving digital landscape of 2026, security compliance has undergone a fundamental shift. Gone are the days when a “check-the-box” mentality sufficed to protect an organization or satisfy a regulator. Today, the complexity of the threat landscape—coupled with a barrage of new regulations like the EU AI Act and updated SEC disclosure requirements—has made manual, spreadsheet-based compliance a liability rather than a strategy.
As the LogicGate team recently noted during this controls compliance webinar, most risk and security leaders find themselves trapped in one of six systemic challenges:
- Lack of visibility into the complete controls environment.
- Struggling to balance internal requirements with external mandates.
- Inefficiency in managing individual control instances.
- Redundant evaluations that drain team resources.
- Lack of actionable insights from compliance data.
- The absence of a data-backed narrative to influence executive budgets.
To move from manual chaos to strategic order, organizations are increasingly turning to GRC automation. This guide explores the modern state of security compliance, how to automate your frameworks, and the real-world impact of solutions like LogicGate’s Controls Compliance Application.
What is Security Compliance or Controls Compliance?
While often used interchangeably, there is a nuanced difference between these two pillars of GRC.
Security Compliance is the process of adhering to external mandates, laws, and industry standards (like SOC 2, ISO 27001, or NIST CSF) to ensure that data is protected, private, and available. It is the set of rules your organization must play by to maintain trust and legality.
Controls Compliance, on the other hand, is the “How.” It refers to the internal mechanisms—policies, technical configurations, and administrative actions—that an organization puts in place to meet those security requirements.
LogicGate’s Solution Engineering Manager, Patrick Ryan, demonstrated how a modern controls compliance application acts as the connective tissue across frameworks, internal standards, and dynamic risk data. It allows you to:
- Centralize a Control Inventory: Establishing a “Global Parent Control” (e.g., Access Termination) that can be applied across different business units or instances.
- Establish Ownership: Moving beyond vague “IT responsibility” to specific metadata, assigning owners, and setting automated frequencies for testing.
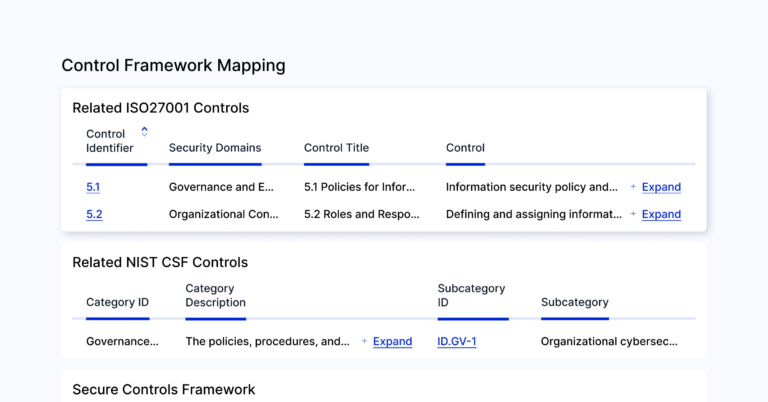
- Interconnect Data: Utilizing a no-code graph database to see how one control (Access Termination) mitigates a specific risk (Unauthorized Access) and satisfies multiple framework requirements (SOC 2, HIPAA, and PCI) simultaneously.
- Real-Time Reporting: Moving beyond lagging “pass/fail” results to actionable program metrics that scale and demonstrate business impact, like automated evidence monitoring and quantified metrics around revenue enabled by framework compliance.
Why Does Security Compliance Matter? The ROI of Resilience
Compliance is no longer just about avoiding fines; it is a value multiplier. Let’s look at some real life tangible examples from LogicGate customers. Organizations that transition from manual “audit cycles” to a state of “ongoing audit readiness” often experience significant improvements.
- Reduce Audit Cycles by 80%: LogicGate customers have access to out-of-the-box control cross-mappings, framework gap analyses, and automated evidence monitoring. By automating these traditionally redundant, time-intensive compliance tasks, teams significantly reduce audit cycles and can shift resources to remediating issues.
- Validate Evidence 65% Faster: Teams leveraging Spark AI Automated Evidence Testing can immediately alert control owners when insufficient documentation is shared and automate extensive, first-pass reviews at scale.
- Save an Average of 1,170 Hours Annually: Through Risk Cloud automations alone, teams reclaim over half a year of FTE time previously spent on manual data entry and follow-up emails. One particular LogicGate customer reported an annual savings of 2,800 hours, allowing them to defer the hiring of one FTE and one contractor.
Beyond the numbers, a mature security compliance posture provides an executive narrative building organizational trust. It allows GRC leaders to walk into a boardroom and show exactly how risk and compliance spending is reducing threats.
Security Compliance: The Ultimate Guide to Automating Your Frameworks
Automation is the only way to keep pace with the 2026 regulatory environment, emerging risks, and shifting customer demands Here is the blueprint for transforming your Security and Framework Compliance Programs into an automated powerhouse.
Step 1: Centralize and Harmonize
The first step is moving out of “disparate spreadsheets.” You must get all controls into a single system of record. LogicGate’s platform allows for bulk imports and bulk linking, ensuring that your existing data is live and actionable within 30 days. By harmonizing controls—identifying where one internal action satisfies three different regulations—you eliminate the “redundant evaluation” trap.
Step 2: Automated Scoping
As shown on screen during LogicGate Controls Compliance webinar, one of the most powerful features of a modern GRC tool is Automated Scoping. When it’s time for a SOC 2 internal audit, you shouldn’t have to manually identify and create tasks for each control and requirement. An automated system pulls in every control designated for that framework, identifies the required evidence, and triggers the assessment process for the correct owners instantly.
Step 3: Automated Evidence Monitoring Collection
Compliance fatigue and lagging insights often come from the “Hey, do you have that file?” discourse and multiple handoffs required as evidence manually progresses from submission to approval. LogicGate solves this challenge by integrating directly with your tech stack to pull and immediately test the latest evidence files. Whether it’s pulling terminated employee lists, cloud configurations from AWS, or access logs from Okta, the system gathers the proof and leverages AI for first-pass review — automatically notifying control owners when issues arise.
“Previously, a user would have to look at the evidence and determine if it’s passing. Now, Spark AI automatically tests it, provides a testing rationale, and marks it as a ‘Pass’ if it satisfies the condition,” explains Pat.
This “Human-in-the-loop” AI approach ensures that the GRC team remains the final authority while the AI handles the heavy lifting of data validation.
Beyond the Checklist: Real-World Impact Story
Let’s look at a real-world example of automation impact. One of LogicGate’s Senior Technical Account Managers shared the story of a large healthcare company he recently worked with. This organization was tasked with managing compliance across 20+ separate entities. Under their old manual system, they were drowning in emails and spreadsheets, struggling to maintain a consistent security posture across a fragmented landscape. By implementing the LogicGate Controls Compliance Application, they achieved:
- Harmonized Control Registers: They created a single source of truth for compliance across more than 20 entities.
- 2,800 Hours Saved Annually: By removing redundant evaluations, automating control owner outreach, and centralizing remediation workflows.
- $500,000 Estimated ROI: These efficiency gains allowed them to defer the hiring of one full-time employee (FTE) and one contractor.
This wasn’t just a compliance win; it’s a business win. It transformed their GRC team from a group of evidence chasers into strategic risk advisors across a complex and dynamic business environment.
Identifying, Assessing, and Mitigating Threats
Security compliance is the foundation of threat management. When your controls are automated, your ability to mitigate threats becomes dynamic.
- Identification: By mapping controls to your risk register(s), you can automatically calculate residual risk scores and see exactly which threats are left exposed if a control fails, ensuring proper prioritization of resources and corrective action.
- Assessment: If an automated test fails (e.g., an employee wasn’t removed from a system within 24 hours of termination), the system doesn’t just log the error, it updates the risk score for “Unauthorized Access” in real-time.
- Mitigation: Find a platform that allows for automated Corrective Action Plans (CAPs). For example, if a finding is raised—even by an external auditor via a PDF—LogicGate’s Spark AI can ingest that document, summarize the gap, and automatically recommend remediation tasks.
Common Compliance Frameworks: Navigating the 2026 Landscape
| Framework | Primary Focus | Industry / Sector | Strategic Insight |
| SOC 2 TSC | Trust Services Criteria (Security, Availability, etc.) | Service Orgs & SaaS | Still the “gold standard” for establishing B2B trust. |
| ISO 27001/2 | Information Security Management Systems (ISMS) | Global Enterprise | The international standard for managing risks to data confidentiality, integrity, and availability. |
| NIST CSF 2.0 | Cybersecurity Risk Management | Federal & Critical Infrastructure | The 2026 go-to for aligning security best practices with business outcomes. |
| HIPAA | Patient Data Privacy & Security | Healthcare | Legally enforceable as a federal law in the United States. |
| PCI DSS | Payment Card Industry Security | Fintech & Retail | Highly specific technical controls for transaction environments. |
| NIST 800-53 | Security & Privacy Controls | Gov & High-Security | Complex, deep-dive controls that complement the NIST CSF and SOC 2. |
| ISO 42001 / EU AI Act | AI Transparency & Governance | AI & Tech Innovators | Already recognized as the international standard for managing AI risks. Aligns nicely with the EU AI Act and other emerging regulations. |
The current landscape is a mix of legacy and widely known as well as emerging mandates. The challenge is understanding the overlap versus gaps, enabling you to strategically prioritize resources to accelerate audit readiness. As seen in the control compliance gap analysis webinar demo, a LogicGate user can compare HIPAA against NIST CSF in seconds.
“I can very easily see where I might already have coverage across two frameworks based on what’s in my environment today,” – LogicGate’s Solution Engineering Manager, Patrick Ryan
The system might highlight that while your technical safeguards are strong, you have a gap in “Physical Safeguards” or “Workstation Use” that needs attention. This insight allows teams to focus their limited resources on the areas that actually move the needle.
Common Challenges on the Road to Compliance
Even with the best intentions, three main hurdles often stall compliance maturity:
| The Challenge | Legacy GRC & Manual Tools | The LogicGate Advantage |
| Siloed Data | Compliance data lives in a vacuum (spreadsheets or disjointed tech acquired by legacy vendors), disconnected from the broader business strategy. | Unified Data: A no-code graph database interconnects controls, risks, and policies for a “single pane of glass” across all GRC use cases. |
| Lack of Flexibility | Requires hard-coding or expensive third-party consultants just to change a simple workflow. | No-Code Agility: Use a drag-and-drop interface to evolve your program as fast as the risk and regulatory landscape changes. |
| Negative User Experience | Clunky interfaces that frustrate “control owners” in HR or DevOps, leading to missing evidence. | User-Centric Design: Intuitive forms and automated notifications make it easy for non-GRC experts to participate. |
LogicGate addresses these common hurdles through its no-code workflow builder. As demonstrated in LogicGate’s compliance webinar, if you want to add a “GRC Review” stage to your process, you simply drag and drop. You don’t need a computer science degree to evolve your program, you just need to know your process.
The Future of Compliance: AI and Automation
The future of GRC is Agentic. We are moving toward a world where AI goes beyond assisting human users with suggestions, and instead, autonomously monitors, tests, and takes actionsLogicGate is leading this charge with Intentional AIwoven into the interface to solve specific problems, like:
- Time-Intensive Control Mapping: Use Spark AI Record Linking Recommendations to automatically map your internal controls directly to other frameworks
- Siloed Compliance Insights: Leverage Spark AI Record Linking Recommendations to identify critical linkages across controls, policies, risks, issues, and much more.
- Delayed Evidence Validation: Use Spark AI Automated Evidence Testing to review evidence and identify gaps as soon as it’s uploaded
- Strategic Corrective Action: Leverage Spark AI Text Assistant to draft correct action plans in a single click.
Conclusion: Compliance is a Continuous State
Security compliance is no longer a destination you reach once a year during an audit; it is a continuous state of readiness. By leveraging unified data, powerful automations, and the strategic insights of the LogicGate Risk Cloud, you can transform your compliance program from a perceived cost center into a value multiplier.
Don’t let manual processes be the weak link in your security chain. Request a demo to learn more about LogicGate’s Controls Compliance Solution.