ISO 27001 and 27002 Frameworks
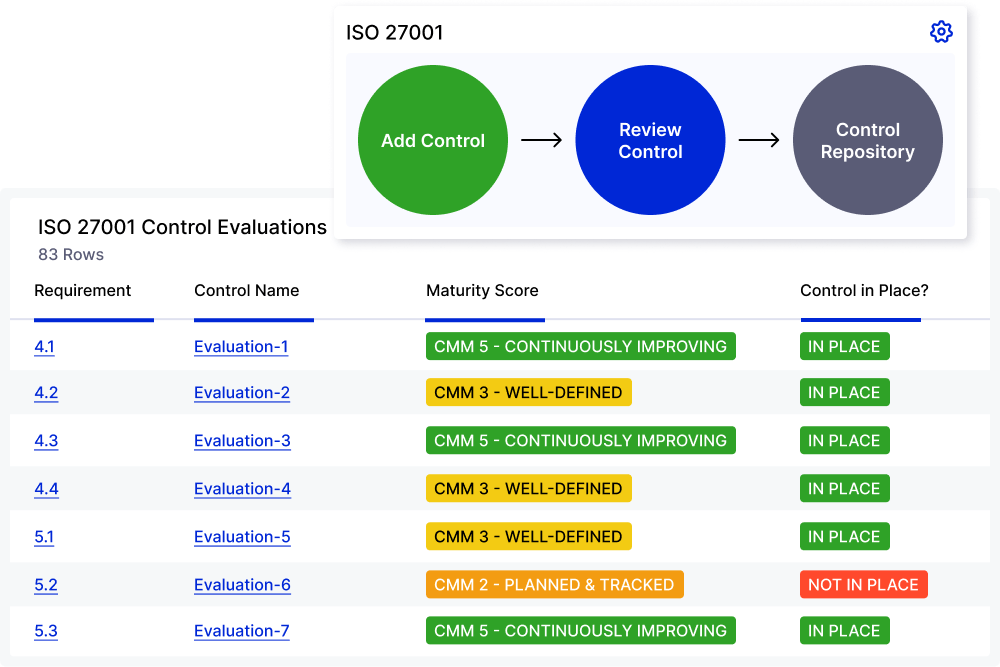
Simplify ISO 27001 & 27002 compliance with mapped controls, automated workflows, and audit‑ready reporting.

Ensure Data Confidentiality, Integrity, and Availability
ISO 27001 is an international standard focused on information security requirements, supported by supplementary standards available through ISO 27002. The goal is to establish and continuously improve a formal Information Security Management System (ISMS)—mitigating risk to systematically protect an organization’s and their customers’ information.
Accelerate ISO 27001* Compliance
Gain customer trust and protect sensitive information by complying with ISO 27001. LogicGate Risk Cloud® enables teams to streamline risk assessments, mitigation planning, control implementation, and ongoing monitoring.
* License not included with platform