LogicGate's Cybersecurity Framework Repository
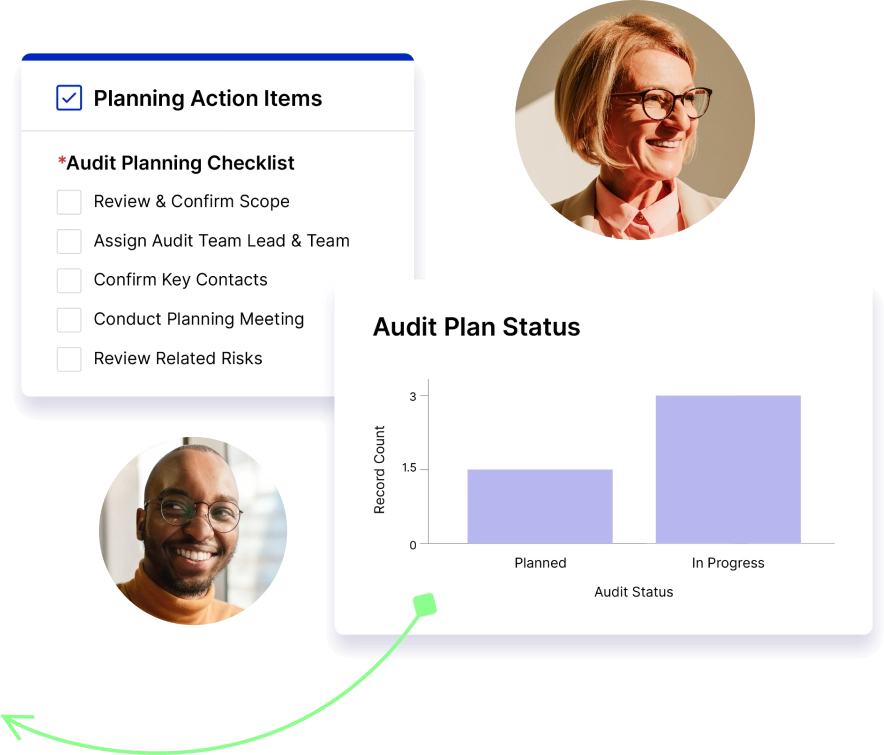
Your entire Cybersecurity Risk program, all in one dynamic system. It's time to take your security to the next level.
Your entire Cybersecurity Risk program, all in one dynamic system. It's time to take your security to the next level.